Case Study: The $25 Million Deepfake Fraud That Fooled Everyone
Reading Time: 9 minutes | Category: Case Studies
In early 2024, a finance employee at a major multinational firm transferred $25.6 million. The order came directly from the company's UK-based Chief Financial Officer during a video conference call. Multiple colleagues were present on the call, and everything seemed normal. Except it wasn't. The CFO, and every other colleague on the call, was a deepfake.
This wasn't a scene from a sci-fi movie. It was a real, devastating attack on the global engineering giant Arup, and it represents a terrifying new frontier in corporate crime. The incident serves as a stark wake-up call for business leaders, CFOs, and security professionals everywhere: the era of deepfake fraud is here, and the stakes are higher than ever.
This case study breaks down the anatomy of this unprecedented heist, the timeline of events, and the critical lessons every organization must learn to avoid becoming the next headline.
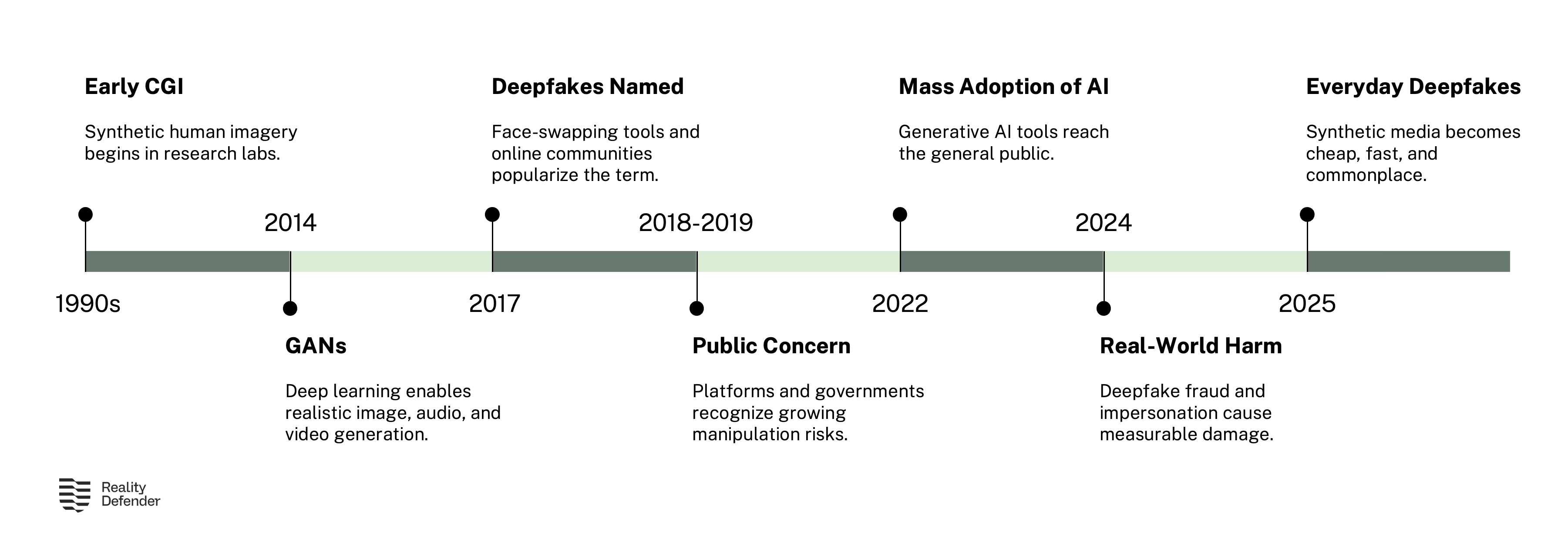
The Soaring Threat of Deepfake Fraud
The Arup case is not an isolated incident; it's the tip of a rapidly growing iceberg. The technology to create convincing deepfakes is no longer confined to Hollywood studios or research labs. It's accessible, effective, and in the hands of sophisticated criminals.
Consider the alarming statistics:
| Statistic | Description | Source |
|---|---|---|
| 1,740% | The surge in deepfake fraud cases in North America between 2022 and 2023. | WEF [1] |
| 680% | The year-over-year rise in general deepfake activity. | Pindrop [2] |
| 53% | The percentage of finance professionals who have been targeted by deepfake schemes. | Medus Survey [3] |
| $500,000 | The average loss per deepfake-related incident for businesses in 2024. | DeepStrike [4] |
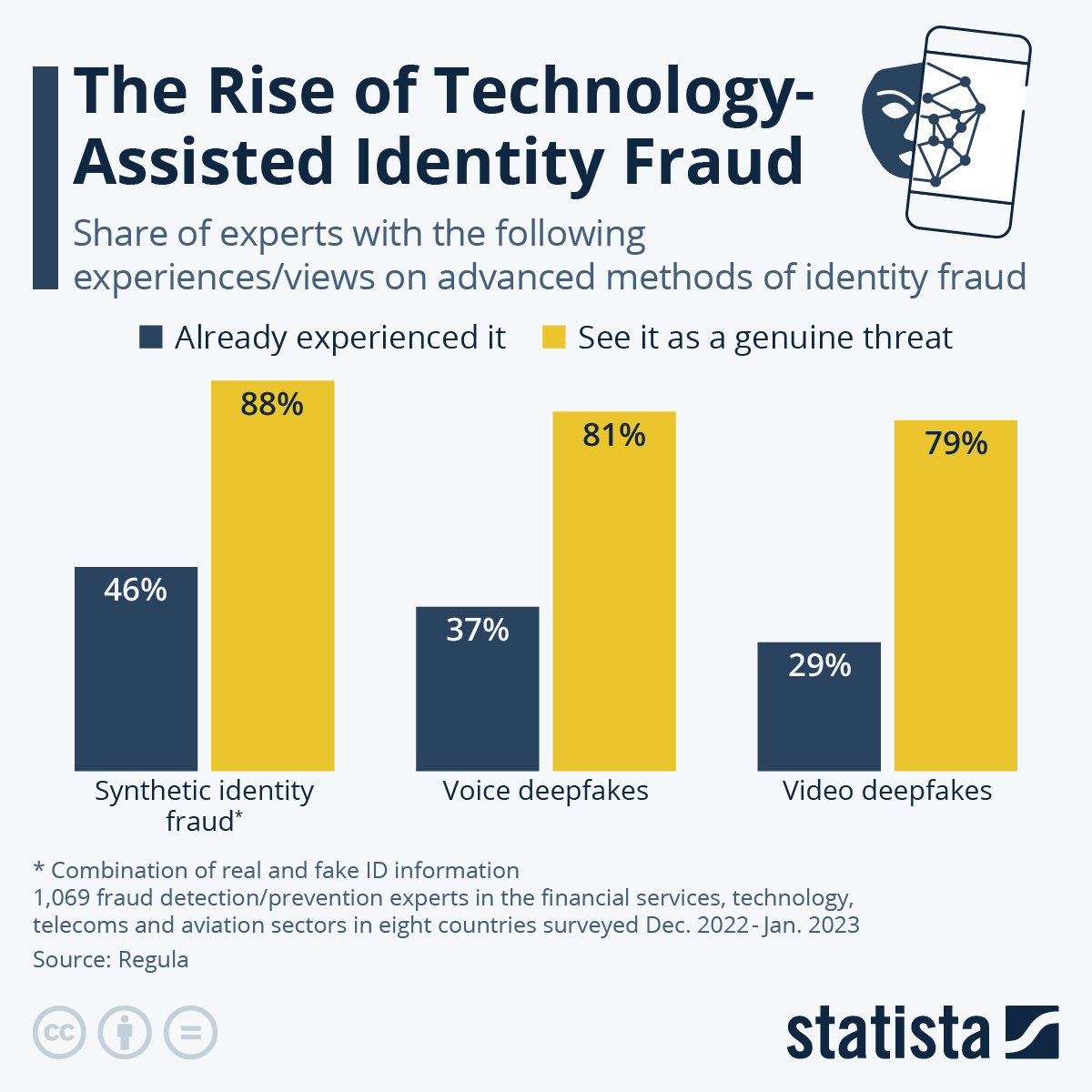
This data paints a clear picture: deepfake fraud is not a future threat, it's a present and escalating danger.
Anatomy of a $25 Million Heist
To understand how to defend against such an attack, we must first dissect how it was executed. The Arup case was a masterclass in what Arup's own CIO, Rob Greig, called "technology-enhanced social engineering."
The Setup: A Phishing Lure
The attack didn't start with a brute-force hack. It started with a simple, familiar tactic: a phishing email. A finance employee in Arup's Hong Kong office received a message purportedly from the company's UK-based CFO. The email mentioned a secret, time-sensitive transaction that needed to be executed.
Initially, the employee was suspicious. The request was unusual. This initial skepticism is a critical human firewall, but the attackers had a plan to dismantle it.
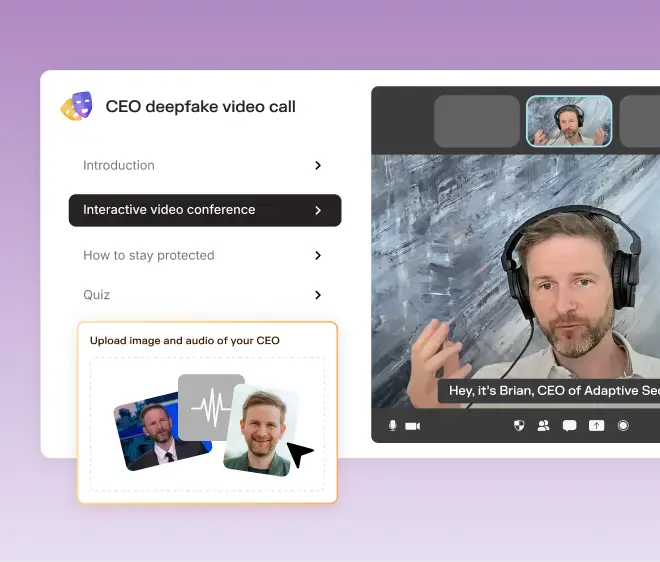
The Execution: The Deepfake Video Conference
To quell the employee's doubts, the fraudsters orchestrated their masterstroke: a multi-person video conference call. When the employee joined the call, they saw not only the CFO but several other familiar colleagues from different departments. They looked and sounded exactly like the real people.
"(In the) multi-person video conference, it turns out that everyone [he saw] was fake," Hong Kong police Senior Superintendent Baron Chan Shun-ching later told the media. [6]
This move was psychologically devastating. The presence of multiple trusted faces created a powerful sense of legitimacy and social proof. The employee's initial doubts were erased, replaced by the urgency of fulfilling a request seemingly validated by the entire senior team. Convinced, the employee made a series of 15 transfers totaling $200 million Hong Kong dollars ($25.6 million USD).
The Aftermath: A Silent Discovery
The crime was only discovered when the employee, after making the transfers, followed up with the company's head office. By then, the money was long gone. Crucially, Arup's CIO Rob Greig clarified that none of their internal systems were compromised. This wasn't a failure of firewalls; it was a failure of perception.
"People were deceived into believing they were carrying out genuine transactions that resulted in money leaving the organization," Greig stated in an interview with the World Economic Forum. [1]
Timeline of the Attack
| Phase | Action | Description |
|---|---|---|
| 1. The Lure | A phishing email is sent to a finance employee. | The email, appearing to be from the UK-based CFO, requests a secret, urgent transaction. |
| 2. The Doubt | The employee is initially suspicious. | The unusual nature of the request raises a red flag. |
| 3. The Deception | A multi-person video call is initiated. | The employee joins a call with what appears to be the CFO and other known colleagues. All are deepfakes. |
| 4. The Convincing | The deepfake colleagues confirm the transaction's legitimacy. | The social proof of seeing multiple trusted faces erases the employee's doubts. |
| 5. The Transfer | The employee executes 15 transfers. | A total of $25.6 million is sent to accounts controlled by the fraudsters. |
| 6. The Discovery | The employee follows up with the head office. | The scam is uncovered, but only after the funds have been transferred. |
4 Critical Lessons for Every Organization
The Arup case provides a sobering, but invaluable, set of lessons for businesses worldwide.
Lesson 1: Adopt a Zero-Trust Mentality for Communication
For decades, the mantra has been "trust, but verify." The new reality is "never trust, always verify." Audio and visual cues are no longer reliable indicators of identity. Organizations must establish strict, out-of-band verification procedures for any sensitive request, especially financial transfers.
- Prevention Strategy: Implement a mandatory policy that any financial transfer request made via email or video call must be independently verified through a separate, secure communication channel (e.g., a direct phone call to a known number, or an in-person confirmation).
Lesson 2: Train for Psychological Manipulation, Not Just Phishing
Standard cybersecurity training often focuses on spotting fake emails. The Arup case shows that the next wave of attacks targets human psychology. Employees need to be trained to recognize the tactics of social engineering, such as urgency, authority, and social proof, especially when enhanced by technology.
- Prevention Strategy: Update employee training to include modules on deepfake threats and technology-enhanced social engineering. Use real-world examples like the Arup case to illustrate the risks.
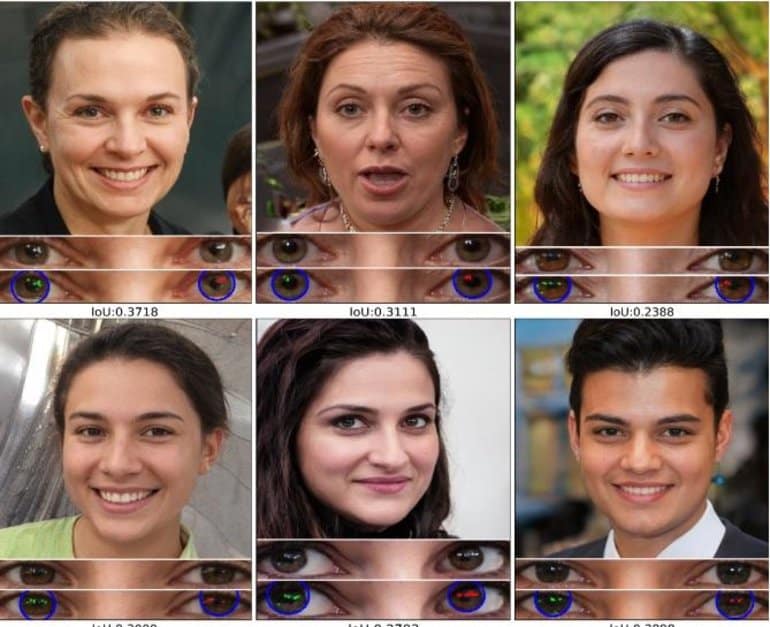
Lesson 3: Technology Must Be Part of the Solution
While the Arup attack exploited human trust, technology is the only scalable way to fight back against AI-driven threats. Relying on human detection alone is no longer viable, as deepfakes become increasingly indistinguishable from reality.
- Prevention Strategy: Invest in real-time deepfake detection solutions. Tools like VerifyReal can analyze video feeds during conference calls, flagging the subtle digital artifacts that deepfakes leave behind but the human eye misses. This provides a critical layer of technological defense.
Lesson 4: Rehearse Your Incident Response
Arup's CIO noted the importance of having a rehearsed response plan. When an attack happens, every second counts. Knowing who to contact, how to assess the breach, and the steps to take to mitigate damage can make the difference between a contained incident and a catastrophe.
- Prevention Strategy: Develop and regularly rehearse an incident response plan specifically for deepfake-related social engineering attacks. Ensure legal, financial, and IT departments are all aligned.
Conclusion: The New Reality of Corporate Security
The $25 million Arup fraud was a watershed moment. It proved that deepfake-driven corporate heists are not theoretical—they are happening now, and they are devastatingly effective. The attackers didn't need to breach a single server; they only needed to breach the trust of a single employee.
As Rob Greig warned, "This happens more frequently than a lot of people realize." Every organization must now operate under the assumption that their leaders' voices and faces can and will be weaponized against them.
Protecting your organization requires a new, multi-layered security paradigm that combines human vigilance with advanced technological defenses. The first step is acknowledging the threat. The next is taking action.
Don't wait to become the next case study. See how VerifyReal can protect your organization from deepfake fraud.
Protect Your Business from Deepfake Fraud
References
[1] World Economic Forum. (2025, February 4). Cybercrime: Lessons learned from a $25m deepfake attack.
[2] Pindrop. (2025, June 12). New Report: Deepfake Fraud Could Surge 162%.
[3] IBM. (n.d.). Are successful deepfake scams more common than we realize?.
[4] DeepStrike. (2025, September 8). Deepfake Statistics 2025: AI Fraud Data & Trends.
[5] Statista. (2024). Share of experts with experience of advanced methods of identity fraud worldwide as of January 2023.
[6] CNN. (2024, February 4). Finance worker pays out $25 million after video call with deepfake ‘chief financial officer’.